CS 211编程代做、代写c/c++,Java程序
CS 211 - Computer Architecture
Instructor: Prof. Santosh Nagarakatte
Assignment 4
Disassembling and Defusing a Binary Bomb
March 25, 2024
Due by April 10, 2024 - 5:00PM
dis·as·sem·ble (vt)
take apart: to take something such as a piece of machinery apart.
– Bing Dictionary
0 Overview
The purpose of Assignment 4 (PA4) is for you to become familiar with x86 64 Instruction Set Architecture (ISA).
The nefarious Dr. Evil has planted a slew of ”binary bombs” on our machines. A binary bomb is a program
that consists of a sequence of phases. Each phase expects you to type a particular string on stdin. If you type the
correct string, then the phase is defused and the bomb proceeds to the next phase. Otherwise, the bomb explodes
by printing ”BOOM!!!” and then terminating. The bomb is defused when every phase has been defused.
There are too many bombs for us to deal with, so we are giving everyone a bomb to defuse. Your mission,
which you have no choice but to accept, is to defuse your bomb before the due date. Good luck, and welcome to
the bomb squad!
1 Instructions
The bombs were constructed specifically for the Linux operating system. You must do this assignment on the iLab
machines. You will not defuse the bomb otherwise and will not get credit.
In fact, there is a rumor that Dr. Evil has ensured the bomb will always blow up if run elsewhere. There are
several other tamper-proofing devices built into the bomb as well, or so they say.
Open an Internet Browser and go to the URL: http://skylake.cs.rutgers.edu:17300. This address is only “visible” when you access it on iLab machines through weblogin. Fill the form up with your NetID
and your email address to get your bomb package. The file that you will get is in the format bombN.tar, where N is
your bomb ID, i.e. ID.
If you haven’t downloaded it in the iLab machines, copy the file to there and untar your bomb into your home
directory.
We recommend that you download no more than two bombs. Copy the bomb that you downloaded into your
iLab account and work with it.
$ tar -xvf bomb<ID>.tar
It will create a directory bomb< ID > that should contain the following files:
1
• bomb: The executable binary bomb
• bomb.c: Source file with the bomb’s main routine
• README: File with the bomb ID and extra information
Your job is to defuse the bomb. You can use many tools to help you with this; please look at the tools section
for some tips and ideas. The best way is to use a debugger to step through the disassembled binary.
The bomb has 9 phases. The phases get progressively harder to defuse, but the expertise you gain as you move
from phase to phase should offset this difficulty. Nonetheless, the latter phases are not easy, so please don’t wait
until the last minute to start. (If you’re stumped, check the hints section at the end of this document.)
The bomb ignores blank input lines. If you run your bomb with a command line argument, for example,
./bomb mysolution.txt
then it will read the input lines from mysolution.txt until it reaches EOF (end of file), and then switch over to
stdin (standard input from the terminal). In a moment of weakness, Dr. Evil added this feature so you don’t have
to keep retyping the solutions to phases you have already defused.
To avoid accidentally detonating the bomb, you will need to learn how to single-step through the assembly code
and how to set breakpoints. You will also need to learn how to inspect both the registers and the memory states.
One of the nice side-effects of doing the lab is that you will get very good at using a debugger. This is a crucial
skill that will pay big dividends the rest of your career.
IMPORTANT: Every time that the bomb explodes, you will lose 0.5 points. It is important that you use
breakpoints and avoid those unnecessary explosions.
2 Resources
There are a number of online resources that will help you understand any assembly instructions you may encounter
while examining the bomb. In particular, the programming manuals for x86 processors distributed by Intel and
AMD can be valuable. They both describe the same ISA, but sometimes one may be easier to understand than the
other.
It is important to realize that the assembly syntax of the instructions on the Intel manual follows the Intel
assembly language, while in the book, in gcc, and in gdb they all use the AT&T assembly language. They are
perfectly interchangable, you can identify the differences in this webpage:
http://asm.sourceforge.net/articles/linasm.html
2.1 Checking your Work
We provided a webpage where you can check your work. Access:
http://skylake.cs.rutgers.edu:17300/scoreboard to verify how many points you have, up to
which phase you have defused the bomb, and so on. You have to be on the iLab machines to access the above link.
3 Tools
There are many ways of defusing your bomb. You can examine it in great detail without ever running the program,
and figure out exactly what it does. This is a useful technique, but it not always easy to do. You can also run it
under a debugger, watch what it does step by step, and use this information to defuse it. This is probably the fastest
way of defusing it.
2
We do make one request, please do not use brute force! You could write a program that will try every possible
key to find the right one, but the number of possibilities is so large that you won’t be able to try them all in time.
There are many tools which are designed to help you figure out both how programs work, and what is wrong
when they don’t work. Here is a list of some of the tools you may find useful in analyzing your bomb, and hints on
how to use them.
• gdb: The GNU debugger is a command line debugger tool available on virtually every platform. You can
trace through a program line by line, examine memory and registers, look at both the source code and
assembly code (we are not giving you the source code for most of your bomb), set breakpoints, set memory
watch points, and write scripts. Here are some tips for using gdb.
– To keep the bomb from blowing up every time you type in a wrong input, you’ll want to learn how to
set breakpoints.
– The CS:APP Student Site has a very handy gdb summary (there is also a more extensive tutorial).
– For other documentation, type help at the gdb command prompt, or type ”man gdb”, or ”info gdb” at a
Unix prompt. Some people also like to run gdb under gdb-mode in emacs.
• objdump -t bomb: This will print out the bomb’s symbol table. The symbol table includes the names of all
functions and global variables in the bomb, the names of all the functions the bomb calls, and their addresses.
You may learn something by looking at the function names!
• objdump -d bomb: Use this to disassemble all of the code in the bomb. You can also just look at individual
functions. Reading the assembler code can tell you how the bomb works. Although objdump -d gives you a
lot of information, it doesn’t tell you the whole story. Calls to system-level functions may look cryptic. For
example, a call to sscanf might appear as:
8048c36: e8 99 f c ff ff call 80488d4 < init + 0x1a0 >
To determine that the call was to sscanf, you would need to disassemble within gdb.
• strings -t x bomb: This utility will display the printable strings in your bomb and their offset within the
bomb.
Looking for a particular tool? How about documentation? Don’t forget, the commands apropos and man
are your friends. In particular, man ascii is more useful than you’d think. If you get stumped, use the course’s
discussion board on Canvas.
4 Submission
You have to e-submit the assignment using Canvas. Your submission should be a tar file named bomb < ID > .tar
that can be extracted using the command:
tar -xf bomb<ID>.tar
Extracting your tar file must give a directory called bomb < ID >. This directory should contain the same
files that you downloaded, along with the file mysolution.txt to defuse the bomb.
To create the tar file that you will submit after finishing your programming assignment, you will use the following command line, in the parent directory of bomb < ID >:
tar -cvf bomb<ID>.tar bomb<ID>/
3
5 Grading
Your grade will be based on how many stages of the bomb you have defused. Be careful to follow all instructions.
If something doesn’t seem right, ask.
6 Collaboration
You are not supposed to assist your friends or other students in solving the bombs. You are required not to use any
online resource other than ones explicitly described above. If in doubt, ask. Keep in mind that your final will test
请加QQ:99515681 邮箱:99515681@qq.com WX:codinghelp
- 龟仙洞酒荣获“中国十八大新名酒”
- instagram自动发帖营销软件,ins群发私信助手工具
- 揭秘广东筑梦人新型材料有限公司负氧离子黄晶板简约而不失随性的生活
- 西部数据通过ASPICE CL3评估认证,满足汽车行业不断变化的需求
- 丰田章男称未来依然需要内燃机 已经启动电动机新项目
- 代做COMP9021、代写Python设计编程
- 全球营销星际商务奇谭:Line群发云控工具是科技魔法的催化剂,引领我进入业务的星际时代
- TG、WS、Zalo、line海外营销乐乐信息 代筛料子软件有哪些?
- COMP3334代做、代写Python程序语言
- TikTok管理层重组,CEO周受资更多监督内容审核
- 全球之星 博主致辞 WhatsApp拉群是我国际业务成功的璀璨明珠
- ins批量群发秘籍!Instagram 2024最新群发软件推荐,Ins引流轻松搞定!
- 精准广告是营销领域的重要一环,而如何在WhatsApp拉群上实现这一目标则是一个值得探讨的话题。
- Instagram涨粉引流方式推荐,Ins出海引流博主营销新助手!
- 数据艺术家TG-WS-LINE云控/自动注册机/筛料拉活人:zalo代筛料子专业服务为您呈现一手数据之美
- 顺峰宝宝开启“透明工厂”时代,儿童化妆品安全可靠再升级
- 五金建材批发网:一站式采购平台,打造高效便捷的建材供应链
- Instagram营销群发软件,Ins一键群发工具,助你实现营销梦想!
- QBUS6820代做、Python编程语言代写
- VDP160直流无刷水泵在水循环冷却应用分析报告
- 全球市场海外拉群攻略:WhatsApp代筛料子推广开创新商机
- Telegram代群发新利器,提高用户互动黏性
- 雪浪云工业知识中台,开启知识管理新篇章
- 专业导师心选WtApp工具专业海外营销高手如何揭示市场趋势谱写商业传奇
- Instagram群发筛选软件,Ins群发注册工具,助你轻松营销!
- 共绘数字化新篇章|谷器数据获评中国移动“2023年度优秀信息化合作伙伴”
- 全球首个微流控专利检索平台-微芯知库正式发布!专访创始人叶嘉明博士
- 《流浪地球2》电影中的数字生命将照进现实?
- 科技大神揭秘:Telegram代拉群营销工具的超能力真实可信,绝对值得一试
- ISLE 2024展会:洲明科技引领LED显示技术创新
推荐
-
 全力打造中国“创业之都”名片,第十届中国创业者大会将在郑州召开
北京创业科创科技中心主办的第十届中国创业
科技
全力打造中国“创业之都”名片,第十届中国创业者大会将在郑州召开
北京创业科创科技中心主办的第十届中国创业
科技
-
 丰田章男称未来依然需要内燃机 已经启动电动机新项目
尽管电动车在全球范围内持续崛起,但丰田章男
科技
丰田章男称未来依然需要内燃机 已经启动电动机新项目
尽管电动车在全球范围内持续崛起,但丰田章男
科技
-
 B站更新决策机构名单:共有 29 名掌权管理者,包括陈睿、徐逸、李旎、樊欣等人
1 月 15 日消息,据界面新闻,B站上周发布内部
科技
B站更新决策机构名单:共有 29 名掌权管理者,包括陈睿、徐逸、李旎、樊欣等人
1 月 15 日消息,据界面新闻,B站上周发布内部
科技
-
 升级的脉脉,正在以招聘业务铺开商业化版图
长久以来,求职信息流不对称、单向的信息传递
科技
升级的脉脉,正在以招聘业务铺开商业化版图
长久以来,求职信息流不对称、单向的信息传递
科技
-
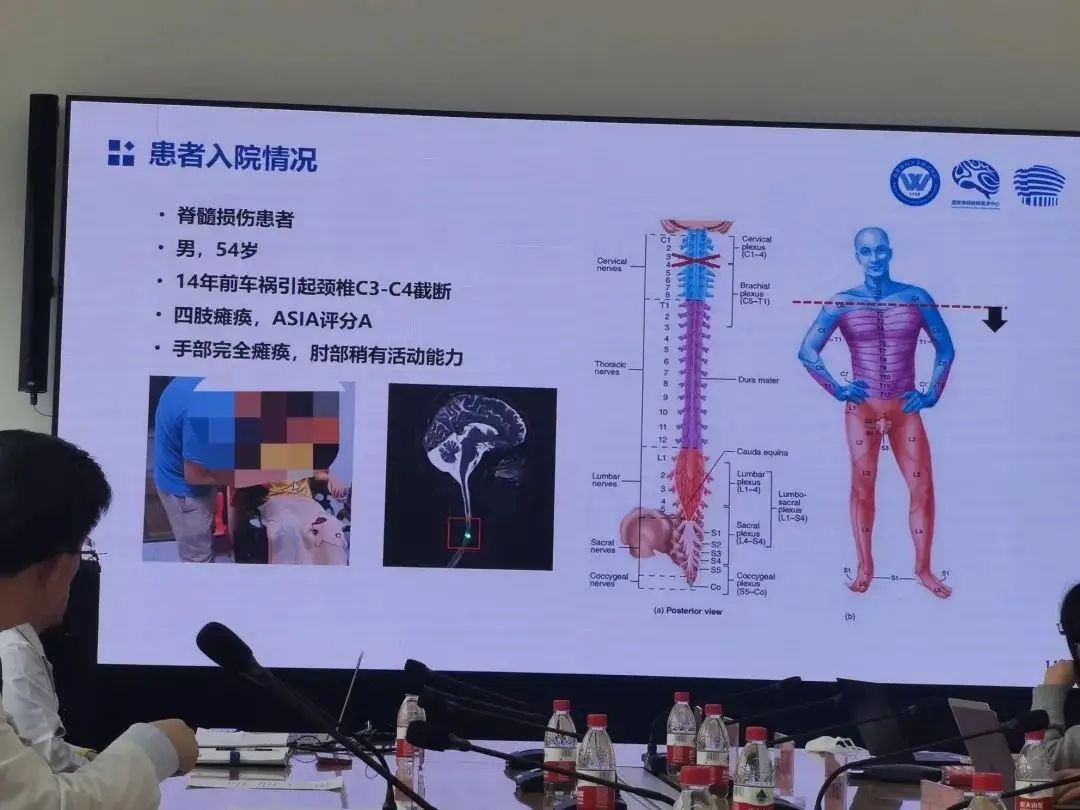 老杨第一次再度抓握住一瓶水,他由此产生了新的憧憬
瘫痪十四年后,老杨第一次再度抓握住一瓶水,他
科技
老杨第一次再度抓握住一瓶水,他由此产生了新的憧憬
瘫痪十四年后,老杨第一次再度抓握住一瓶水,他
科技
-
 如何经营一家好企业,需要具备什么要素特点
我们大多数人刚开始创办一家企业都遇到经营
科技
如何经营一家好企业,需要具备什么要素特点
我们大多数人刚开始创办一家企业都遇到经营
科技
-
 智慧驱动 共创未来| 东芝硬盘创新数据存储技术
为期三天的第五届中国(昆明)南亚社会公共安
科技
智慧驱动 共创未来| 东芝硬盘创新数据存储技术
为期三天的第五届中国(昆明)南亚社会公共安
科技
-
 苹果罕见大降价,华为的压力给到了?
1、苹果官网罕见大降价冲上热搜。原因是苹
科技
苹果罕见大降价,华为的压力给到了?
1、苹果官网罕见大降价冲上热搜。原因是苹
科技
-
 创意驱动增长,Adobe护城河够深吗?
Adobe通过其Creative Cloud订阅捆绑包具有
科技
创意驱动增长,Adobe护城河够深吗?
Adobe通过其Creative Cloud订阅捆绑包具有
科技
-
 疫情期间 这个品牌实现了疯狂扩张
记得第一次喝瑞幸,还是2017年底去北京出差的
科技
疫情期间 这个品牌实现了疯狂扩张
记得第一次喝瑞幸,还是2017年底去北京出差的
科技

